If your service was recently onboarded to VMware Cloud services, you might have some legacy service accounts for backward compatibility. It’s strongly recommended that you incrementally switch to using server to server OAuth apps which authenticate with more secure VMware Cloud services access tokens. See How to Replace a Service Account with a Server to Server App?.
What Are Service Accounts?
- A service account uses an Tanzu Observability API token to authenticate.
- By default, service accounts don’t have any permissions, even view permissions. Users with the Admin service role must explicitly grant each service account only the permission required for the task that’s being automated (least required privilege). There’s no limit on the number of service accounts that you can create in your service instance.
As a user with the Admin service role, you generate (and revoke, if needed) the API tokens for the service account. It’s also possible to deactivate a service account completely.
How Service Accounts Work
If you plan to set up an integration that uses a proxy authentication with a Tanzu Observability API token, you must create a service account with the Proxies permission and generate an API token for it.
- Create a service account from the UI. The service account name must be unique.
- Assign the service account with the Proxies permission.
-
Set up the proxy in your integration to pass the API token of the service account.
The proxy authenticates seamlessly to the API without embedding secret keys or user credentials in your instance, image, or application code.
You can disable a service account if you temporarily don’t need it, or you can delete the service account permanently.
Create a Service Account
Service accounts are created in Tanzu Observability.
- Log in to your service instance as a user with the Admin service role.
- From the gear icon on the toolbar, select Accounts.
- Click the Service Accounts tab and click Create New Account.
- On the New Service Account page, specify the account details and click Create.
| Field | Description |
|---|---|
| Account ID | ID of the account. We prefix this ID with sa::. A service account name must be unique. Tanzu Observability converts a service account ID to lower case to avoid confusion that can result from almost identical account names (e.g. Service-1 and service-1). Users can type upper case or lower case. |
| Tokens | List of API tokens that the service account can use to authenticate to the Tanzu Observability service instance.
|
| Permissions | Individual permissions assigned to this service account. Assign the service account with the Proxies permission, so that you can use it for the proxy setup of an integration that authenticates with a Tanzu Observability API token. |
Deactivate or Activate a Service Account
You can temporarily (or permanently) deactivate a service account. When an account is deactivated, none of the corresponding tokens work.
You can activate or deactivate a service account from the Service Accounts page or from the Edit Service Account page.
To activate or deactivate an account from the Service Accounts page:
|
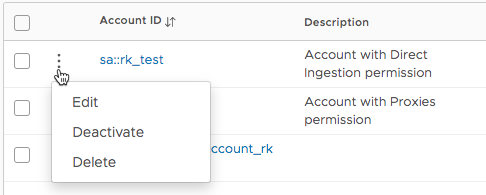 |
To activate or deactivate an account from the Edit Service Account page:
|
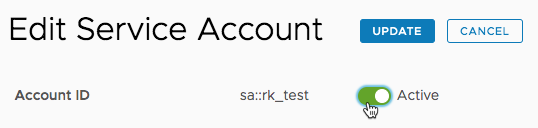 |
Grant or Revoke Permissions
You can grant permissions to a service account when you create the account or add permissions later from the Service Accounts page or from the Edit Service Account page.
The following example shows two ways of explicitly granting or revoking permissions for service accounts.
To grant or revoke permissions from the Service Accounts page:
|
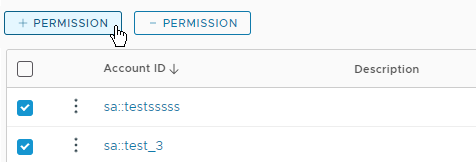 |
To grant or revoke permissions from the Edit Service Account page:
|
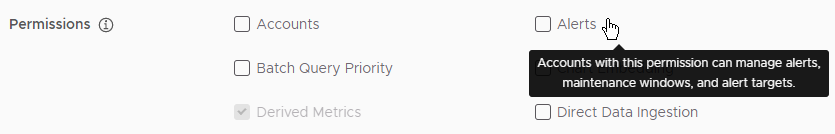 |